Executive Summary: In today's rapidly evolving cybersecurity landscape, the term "ultra antivirus" represents a new generation of security solutions that transcend traditional malware detection. Ultra antivirus software combines multi-layered defense mechanisms, artificial intelligence-driven threat analysis, system optimization capabilities, and proactive vulnerability management to deliver comprehensive protection against sophisticated cyber threats. This article explores what distinguishes ultra antivirus solutions from conventional security software, examining their advanced features, modern threat mitigation strategies, selection criteria, enterprise applications, performance optimization capabilities, and future trends shaping the cybersecurity industry through 2026 and beyond.
What Makes an Antivirus Solution "Ultra"?
The designation "ultra" in antivirus software signifies a paradigm shift from reactive signature-based protection to proactive, intelligent security ecosystems. Ultra antivirus solutions represent the pinnacle of desktop security technology, incorporating advanced threat intelligence, behavioral analysis, and system optimization features that work synergistically to protect and enhance computer performance. According to 2026 cybersecurity research, the most effective security solutions integrate multiple protection layers while maintaining minimal system impact—a hallmark of truly ultra-grade antivirus software.
Beyond Basic Malware Detection
Traditional antivirus software relies primarily on signature-based detection, comparing files against databases of known malware signatures. While this approach remains foundational, ultra antivirus solutions extend far beyond these basic capabilities. Real-time protection in ultra antivirus systems actively monitors system activities, file operations, and network communications to detect and neutralize threats including viruses, ransomware, spyware, trojans, and rootkits before they can execute malicious payloads.
What truly distinguishes ultra antivirus is its implementation of advanced heuristic analysis and behavioral monitoring. These technologies enable the software to identify previously unknown threats—zero-day exploits and polymorphic malware—by analyzing suspicious behaviors and code patterns rather than relying solely on signature matching. For example, if a program attempts to encrypt multiple files rapidly or modify critical system settings without authorization, behavioral monitoring flags this activity as potentially malicious even if the program has never been cataloged in threat databases.
Industry data from 2025 indicates that behavioral detection methods catch approximately 30-40% more threats than signature-only approaches, particularly against newly developed malware variants. This proactive stance transforms antivirus from a reactive shield into an intelligent guardian that adapts to emerging threats in real-time.
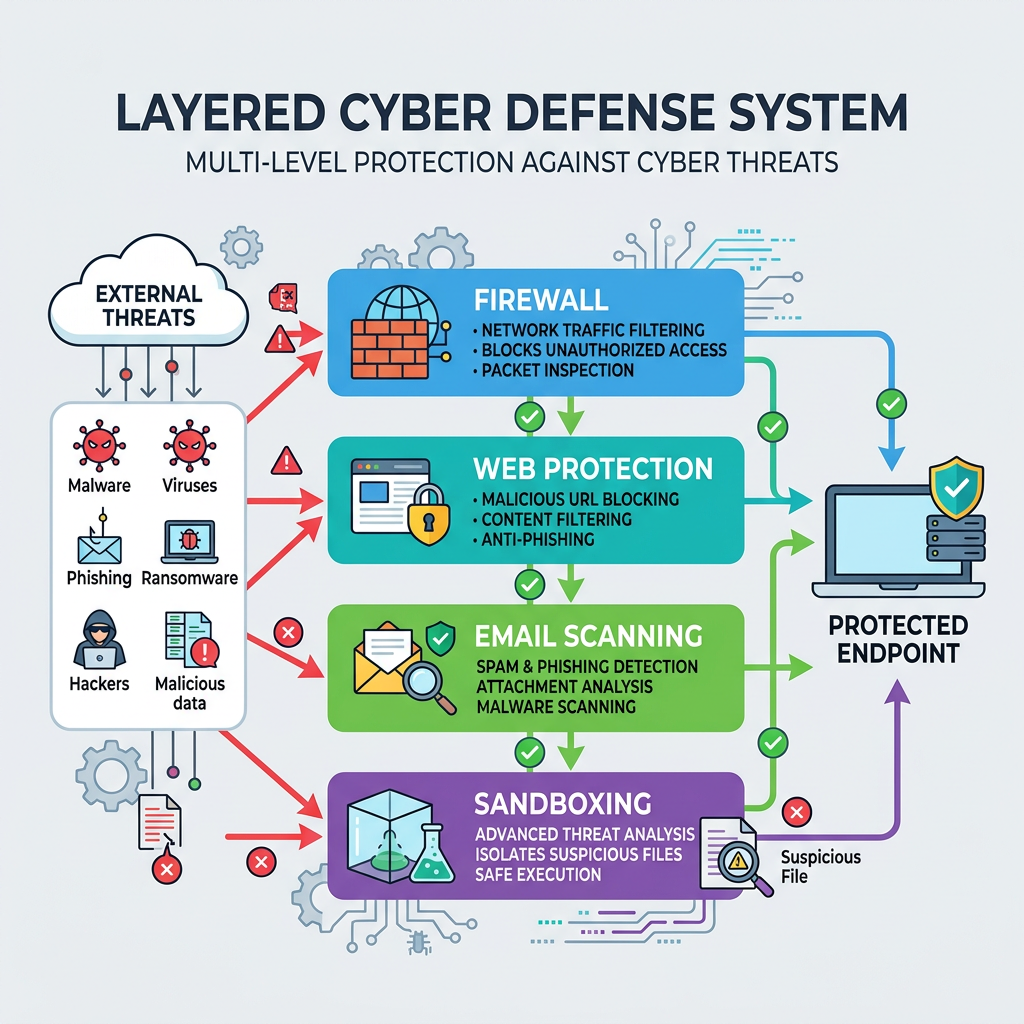
Multi-Layered Defense Systems
Ultra antivirus solutions architect security through multiple integrated protection layers, creating redundant safeguards that compensate for potential weaknesses in any single defense mechanism. The first layer typically consists of a firewall component that monitors and controls incoming and outgoing network traffic based on predetermined security rules, preventing unauthorized access attempts and blocking malicious network communications.
The second critical layer involves web protection and email scanning capabilities. Web protection modules analyze URLs in real-time, blocking access to known phishing sites, malware distribution networks, and fraudulent domains before users can inadvertently download threats. Email scanning scrutinizes attachments and embedded links, quarantining suspicious content before it reaches the inbox. According to cybersecurity whitepapers on advanced threat isolation published in 2026, these preventive measures stop approximately 70% of malware infections at the entry point, before threats can establish persistence on the system.
Perhaps the most sophisticated layer in ultra antivirus architecture is sandboxing technology. When the system encounters a suspicious file of uncertain origin, sandboxing isolates it within a virtualized environment—a "sandbox"—where it can be executed and observed without risking the actual system. Security analysts and automated systems monitor the file's behavior within this controlled space, determining whether it exhibits malicious characteristics before allowing it to interact with the real operating system. This technique proves particularly effective against advanced persistent threats and zero-day exploits that might evade traditional detection methods.
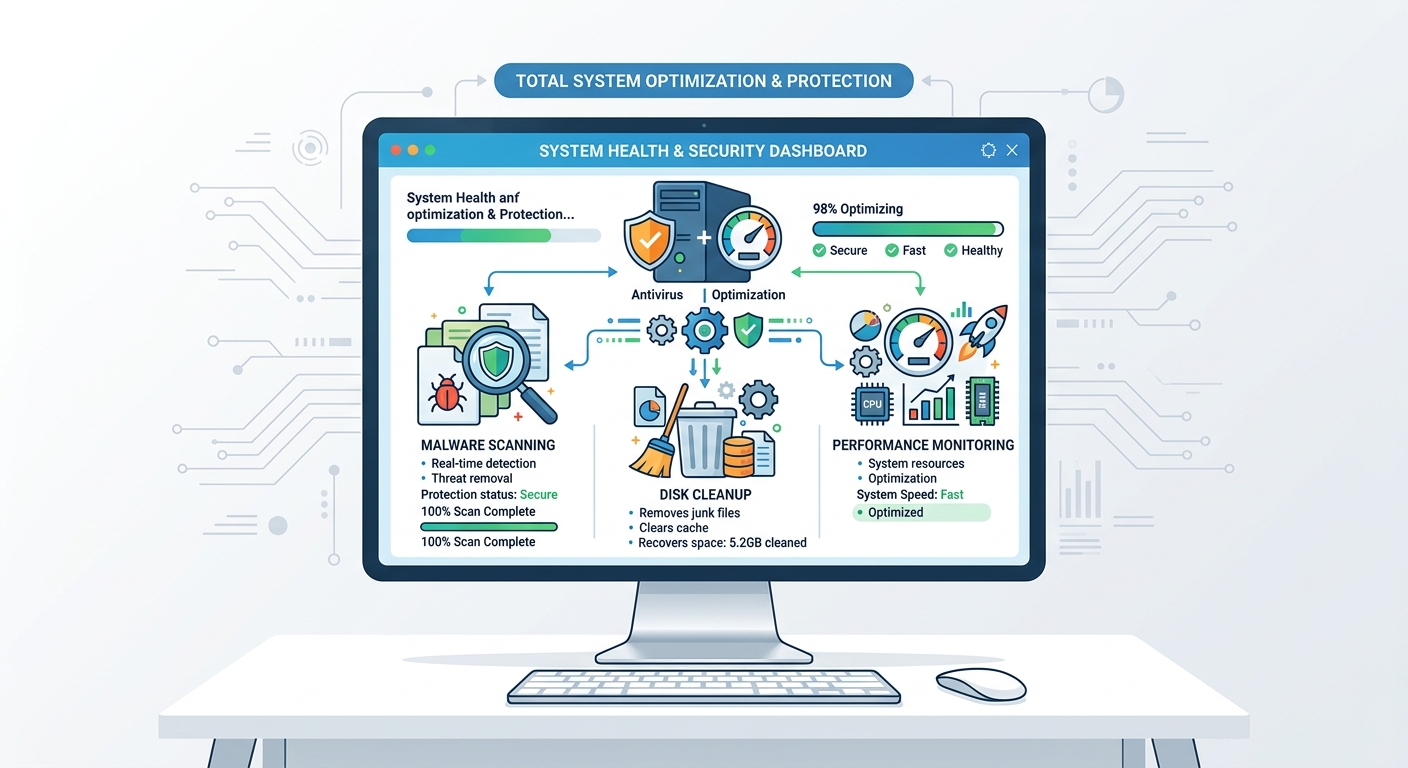
Inclusion of System Optimization Tools
A defining characteristic of ultra antivirus software is the integration of system optimization and maintenance tools alongside security features. Recognizing that computer performance and security are interconnected, leading ultra antivirus solutions include capabilities such as disk cleanup, startup management, registry optimization, and performance boosters.
Disk cleanup features identify and remove temporary files, browser cache, system logs, and redundant data that accumulate over time, freeing valuable storage space and potentially eliminating hiding places for malware. Startup management tools allow users to control which programs launch automatically when the computer boots, reducing boot times and preventing resource-hogging applications from degrading system responsiveness.
Performance monitoring dashboards provide real-time visibility into CPU usage, memory consumption, disk activity, and network bandwidth, helping users identify resource bottlenecks and optimize system configuration. Some ultra antivirus solutions even include driver updaters and software patch management to ensure all system components remain current and secure.
This holistic approach recognizes that a secure computer must also be a well-maintained, efficiently operating machine. By combining protection and optimization in a single solution, ultra antivirus software delivers comprehensive digital health management for desktop systems.
Key Features of Ultra Antivirus Software
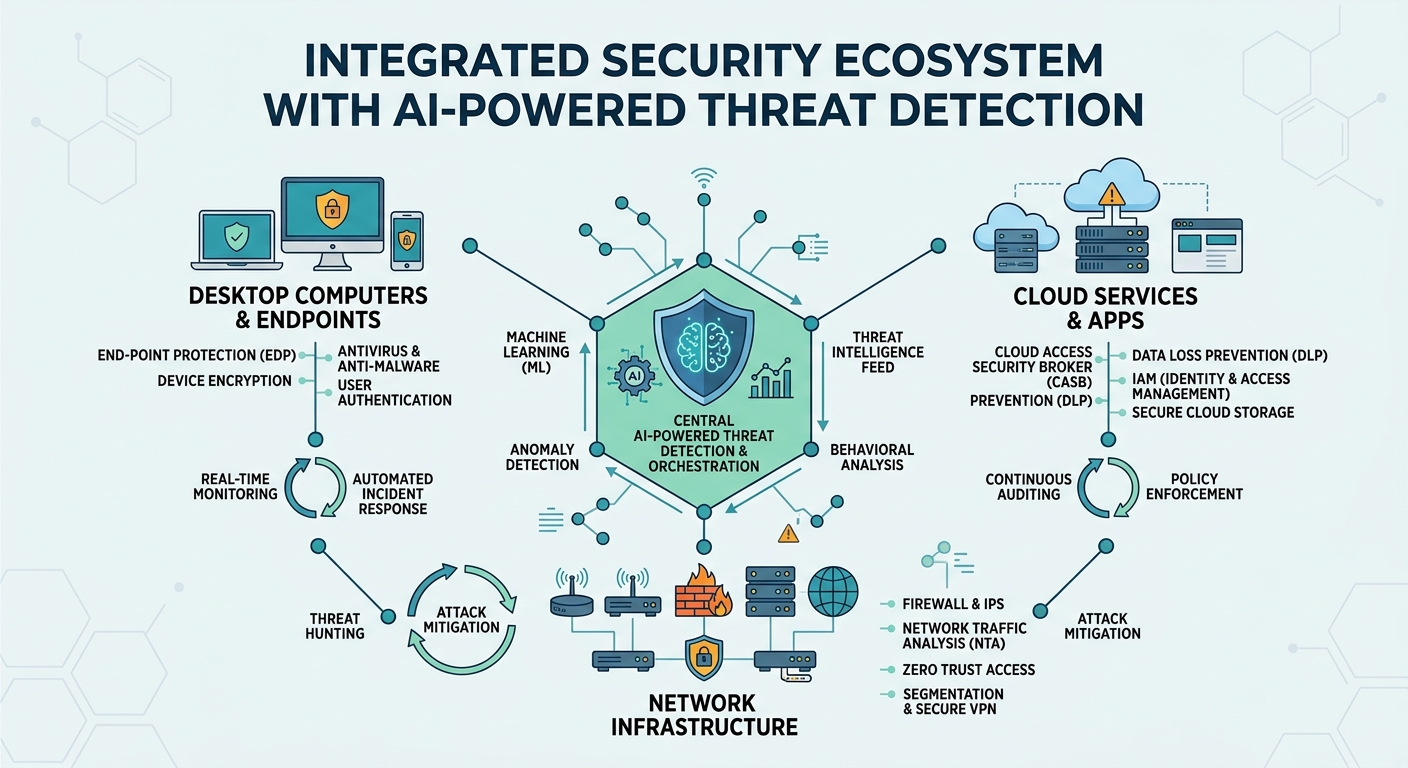
Ultra antivirus software distinguishes itself through an advanced feature set that leverages cutting-edge technologies including artificial intelligence, cloud-based threat intelligence, and optimized scanning engines. These capabilities work in concert to provide superior protection while minimizing system performance impact—a critical balance that separates premium solutions from basic security software.
AI and Machine Learning in Threat Detection
The integration of artificial intelligence and machine learning represents perhaps the most significant advancement in modern antivirus technology. Unlike traditional rule-based systems that require explicit programming for each threat type, AI-powered antivirus solutions learn continuously from vast global threat databases, identifying patterns and correlations that human analysts might miss.
Machine learning algorithms analyze millions of file characteristics—code structure, API calls, registry modifications, network behaviors—to develop sophisticated models of malicious versus benign software. As these systems process more data, their accuracy improves through iterative refinement. According to 2026 industry reports, AI-enhanced detection engines demonstrate detection rates 15-25% higher than conventional signature-based systems, with significantly lower false positive rates.
The continuous learning capability proves particularly valuable against polymorphic malware that constantly mutates its code to evade detection. AI systems recognize the underlying behavioral patterns and structural characteristics that persist across mutations, enabling identification of malware families even when specific signatures change. Cloud connectivity allows these systems to share threat intelligence globally, so when one user encounters a new threat anywhere in the world, the entire user base benefits from updated protection within minutes.
Furthermore, AI-driven predictive analysis can identify emerging threat trends before they become widespread, enabling proactive defense postures rather than reactive responses. This forward-looking capability represents a fundamental shift in cybersecurity strategy, moving from "detect and respond" to "predict and prevent."
Lightweight Design and Performance Optimization
A common criticism of antivirus software has historically been its tendency to consume excessive system resources, slowing computer performance and frustrating users. Ultra antivirus solutions address this concern through efficient scanning engines that minimize CPU and memory usage while maintaining comprehensive protection.
Modern ultra antivirus software employs several optimization techniques. Intelligent scheduling runs intensive scans during idle periods when users aren't actively working, preventing performance degradation during critical tasks. Incremental scanning focuses on changed or new files rather than repeatedly scanning unchanged system files, dramatically reducing scan times. Cloud-assisted scanning offloads resource-intensive analysis to remote servers, allowing lightweight client software to deliver powerful protection without burdening local hardware.
According to performance benchmarks published in 2025, leading ultra antivirus solutions typically consume less than 1-2% of CPU resources during normal operation and complete full system scans 40-60% faster than previous-generation software. Memory footprints have similarly decreased, with many solutions operating efficiently within 150-200MB of RAM—a fraction of what older security software required.
For users seeking to maximize these benefits, configuring antivirus settings appropriately proves essential. 360 Total Security exemplifies this optimization approach, offering customizable scanning modes, scheduling options, and resource allocation settings that allow users to balance protection intensity with system performance based on their specific needs and hardware capabilities.
Proactive Vulnerability and Patch Management
Beyond detecting active malware, ultra antivirus solutions incorporate proactive vulnerability scanning capabilities that identify potential security weaknesses before they can be exploited. These systems regularly scan installed software, operating system components, and device drivers to detect outdated versions with known security vulnerabilities.
When vulnerabilities are discovered, ultra antivirus software provides automated recommendations for updates and fixes, often including direct links to official patches or update mechanisms. Some solutions even integrate automated patch deployment for critical security updates, ensuring systems remain protected against newly disclosed vulnerabilities without requiring user intervention.
This proactive approach proves particularly valuable given that cybercriminals increasingly target known vulnerabilities in popular software. According to 2026 threat intelligence reports, approximately 60% of successful cyberattacks exploit vulnerabilities for which patches were available but not applied. By systematically identifying and addressing these weaknesses, ultra antivirus solutions close security gaps that might otherwise provide entry points for attackers.
Additionally, vulnerability management features often extend to network security, scanning for weak passwords, unsecured wireless networks, and misconfigured security settings that could compromise system integrity. This comprehensive approach to security hygiene elevates ultra antivirus from simple malware detection to holistic system protection.
How Ultra Antivirus Protects Against Modern Threats
The contemporary threat landscape has evolved dramatically beyond simple viruses and worms. Today's cybercriminals deploy sophisticated attack vectors including zero-day exploits, advanced phishing campaigns, ransomware-as-a-service, and advanced persistent threats (APTs) that can remain undetected for months. Ultra antivirus solutions employ cutting-edge technologies specifically designed to counter these modern threat categories.
Defense Against Zero-Day and Unknown Threats
Zero-day attacks exploit previously unknown vulnerabilities for which no patch or signature exists, representing one of the most dangerous threat categories. Traditional signature-based antivirus proves ineffective against these attacks since, by definition, no signature has been created. Ultra antivirus solutions counter zero-day threats through behavioral analysis and cloud-based threat intelligence.
Behavioral analysis monitors program activities in real-time, flagging suspicious actions that deviate from normal application behavior. For example, if a document editor suddenly attempts to encrypt hundreds of files, modify system boot settings, or establish unauthorized network connections, behavioral monitoring recognizes these as potential ransomware indicators regardless of whether the specific malware variant has been cataloged.
Cloud-based threat intelligence amplifies this protection by aggregating behavioral data from millions of endpoints worldwide. When suspicious activity is detected on any protected system, that intelligence is instantly shared across the entire user base, creating a collective defense network that responds to emerging threats in near real-time. According to cybersecurity experts, this collaborative approach reduces the window of vulnerability for zero-day exploits from weeks or months to mere hours.
Dr. Elena Kovacs, a leading cybersecurity researcher, emphasizes: "Proactive defense mechanisms that don't rely on prior knowledge of specific threats represent the future of endpoint security. Behavioral analysis and machine learning allow security systems to recognize the characteristics of malicious activity even when the specific attack vector is entirely novel."
Enhanced Web and Email Protection
Phishing attacks and malicious web content remain among the most common infection vectors, with 2026 statistics indicating that over 90% of successful breaches begin with a phishing email. Ultra antivirus solutions implement real-time blocking of malicious websites and attachments through multiple protective layers.
Web protection modules maintain continuously updated databases of known malicious domains, phishing sites, and malware distribution networks. When users attempt to access these sites, the antivirus intercepts the connection and displays warning messages, preventing exposure to threats. More advanced systems employ URL reputation analysis, evaluating factors such as domain age, registration patterns, hosting infrastructure, and content characteristics to identify potentially malicious sites even before they're formally cataloged.
Email protection scrutinizes incoming messages for suspicious characteristics including spoofed sender addresses, malicious attachments, and embedded links to phishing sites. Advanced content analysis examines email body text for social engineering tactics commonly used in phishing campaigns, such as urgency language, requests for credentials, or unusual financial requests.
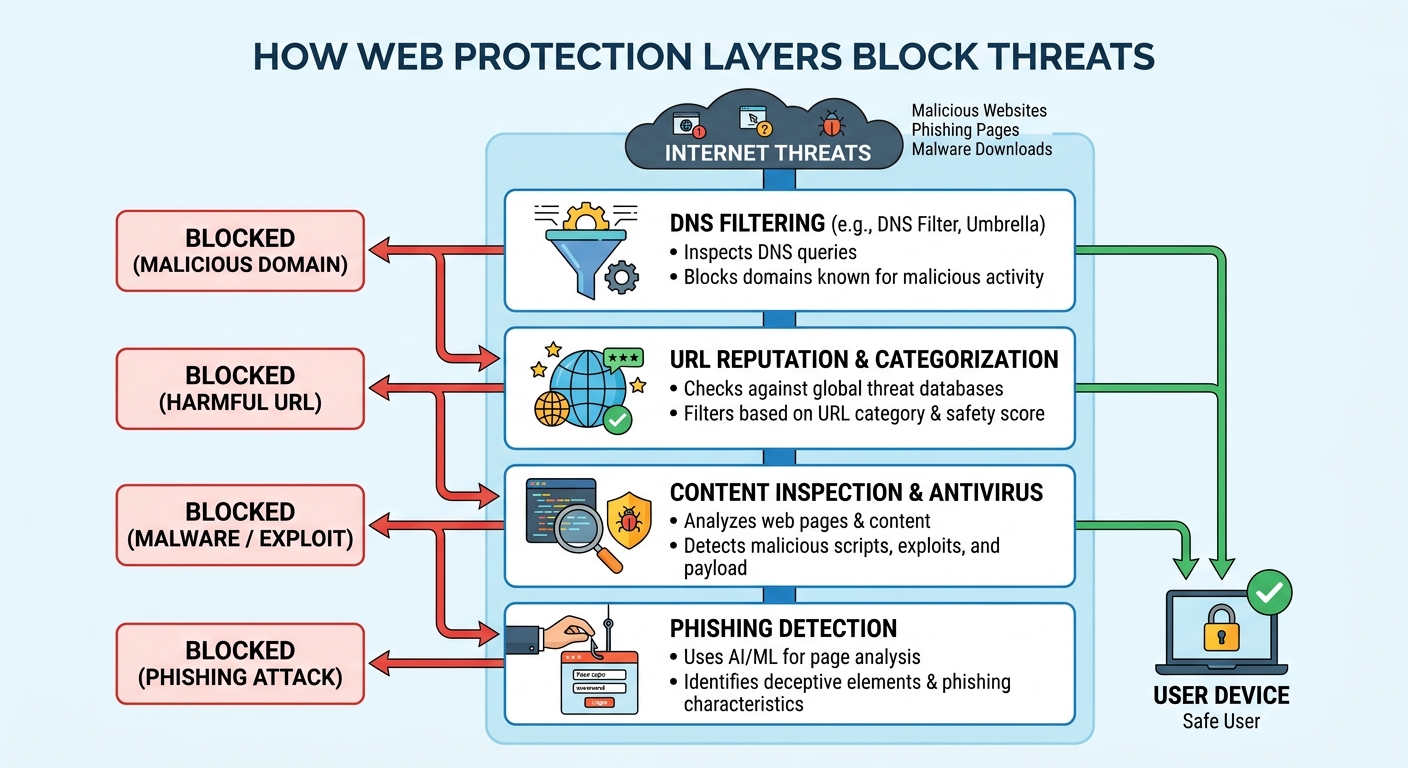
Attachment sandboxing provides an additional safeguard by executing suspicious email attachments in isolated environments before allowing them to interact with the actual system. This multi-layered approach creates overlapping defenses that significantly reduce the likelihood of successful phishing attacks.
Mitigating Advanced Persistent Threats (APTs)
Advanced Persistent Threats represent sophisticated, long-term intrusions typically conducted by well-resourced threat actors targeting specific organizations or individuals. Unlike opportunistic malware that seeks quick exploitation, APTs establish persistent access and conduct reconnaissance over extended periods, often remaining undetected for months or years.
Ultra antivirus solutions counter APTs through long-term monitoring and anomaly detection capabilities that identify subtle behavioral patterns indicative of sustained attacks. These systems establish baselines of normal system and network activity, then flag deviations that might indicate unauthorized access, data exfiltration, or lateral movement within networks.
Key APT detection capabilities include monitoring for unusual outbound network connections, detecting privilege escalation attempts, identifying suspicious scheduled tasks or registry modifications, and recognizing patterns of data aggregation that might precede exfiltration. Machine learning algorithms prove particularly effective at identifying these subtle indicators that human analysts might overlook in the vast volume of system events.
| Ultra Antivirus Solution | Behavioral Monitoring | Network Anomaly Detection | Privilege Escalation Alerts | Data Exfiltration Prevention |
|---|---|---|---|---|
| 360 Total Security | Advanced real-time monitoring | Comprehensive network analysis | System-level alerts | Outbound traffic monitoring |
| Enterprise Solution A | Advanced with SIEM integration | Deep packet inspection | Multi-level alerting | DLP integration |
| Enterprise Solution B | AI-powered behavioral analysis | Machine learning anomaly detection | Automated response workflows | Encrypted traffic analysis |
| Premium Consumer Solution | Standard behavioral monitoring | Basic network protection | Limited alerting | Basic outbound filtering |
While APT detection historically required enterprise-grade security solutions, modern ultra antivirus software increasingly incorporates these capabilities for desktop users, particularly those in high-risk categories such as journalists, activists, or business executives who might be targeted by sophisticated threat actors.
Choosing the Right Ultra Antivirus for Your Needs
Selecting an appropriate ultra antivirus solution requires careful evaluation of multiple factors including protection effectiveness, system compatibility, performance impact, feature set, and cost considerations. The optimal choice varies significantly based on whether you're protecting a home computer, small business network, or enterprise infrastructure.
Assessing Protection Levels and Certification
When evaluating ultra antivirus solutions, independent laboratory test results and certifications provide objective measures of protection effectiveness. Reputable testing organizations such as AV-TEST, AV-Comparatives, and SE Labs conduct rigorous evaluations of antivirus software, measuring detection rates, false positive rates, performance impact, and usability.
The VB100 certification from Virus Bulletin represents a baseline standard, confirming that software successfully detects all "in-the-wild" malware without generating false positives. However, ultra antivirus solutions should exceed this minimum threshold, demonstrating superior performance in advanced threat detection categories including zero-day exploits, ransomware, and phishing protection.
According to 2026 AV-TEST evaluations, top-tier ultra antivirus solutions consistently achieve detection rates above 99.5% for both known and zero-day malware, while maintaining false positive rates below 0.5%. Performance impact scores should indicate minimal system slowdown during scans and normal operation. When comparing solutions, prioritize those with recent test results from multiple independent labs, as this provides the most comprehensive assessment of real-world protection capabilities.
Additionally, consider whether the solution has received industry certifications such as ICSA Labs certification, Checkmark certification, or Microsoft's Windows Security Center compatibility verification, all of which validate that the software meets established security and compatibility standards.
Compatibility with Your Operating System and Devices
Ultra antivirus solutions must provide robust protection for your specific computing environment. For desktop users, this primarily means ensuring support for Windows or macOS operating systems with versions compatible with your current OS release. It's critical to verify that the antivirus software is optimized for your specific OS version, as outdated or incompatible software may fail to provide adequate protection or cause system instability.
When evaluating desktop antivirus solutions, pay careful attention to minimum system requirements including processor speed, RAM, available disk space, and supported OS versions. Ultra antivirus software should operate efficiently within your hardware constraints without causing performance degradation. Solutions designed with lightweight architectures prove particularly valuable for older computers or systems with limited resources.
For users managing multiple computers, consider whether the solution offers multi-device licenses that allow protection of several machines under a single subscription. However, it's essential to understand the scope of protection offered. Some antivirus providers market "multi-device" solutions that include mobile and web protection, but if you're specifically seeking desktop security, verify that the solution provides comprehensive Windows or macOS protection rather than diluting focus across multiple platforms.
Important Note: When selecting desktop antivirus solutions, focus on providers that specialize in comprehensive PC protection. Some solutions attempt to cover too many platforms with varying levels of effectiveness. For optimal desktop security, prioritize solutions with proven track records specifically in Windows and macOS environments.
Evaluating Cost vs. Value: Free and Paid Options
The antivirus market offers both premium paid solutions and robust free alternatives, creating important cost-benefit considerations. Paid antivirus software typically includes advanced features such as ransomware protection, firewall management, VPN services, password managers, parental controls, and priority customer support. Premium solutions often provide more frequent updates, lower false positive rates, and enhanced detection capabilities for sophisticated threats.
However, free antivirus solutions have evolved significantly and can provide excellent protection for many users, particularly home users and small businesses with limited budgets. The key is distinguishing between truly robust free solutions and limited "freemium" offerings that restrict essential features to drive paid upgrades.
360 Total Security exemplifies a world-leading free antivirus solution that delivers comprehensive protection without artificial feature limitations. Its core advantages include multiple antivirus engines for enhanced detection, real-time protection against malware and ransomware, system cleanup and optimization tools, startup management, and regular automatic updates—all available in the free version.
Unlike many "free" antivirus solutions that constantly prompt users to upgrade or restrict critical features, 360 Total Security provides genuine full-featured protection suitable for home users, small businesses, and even some enterprise applications. The integrated system optimization tools—including disk cleanup, privacy protection, and performance boosters—deliver additional value beyond security, helping maintain computer health and responsiveness.
When evaluating cost versus value, consider your specific needs: Do you require advanced features like VPN or password management, or is core malware protection and system optimization sufficient? For many users, a robust free solution like 360 Total Security provides all necessary protection and performance tools without ongoing subscription costs, making it an optimal choice for budget-conscious users who refuse to compromise on security quality.
The Role of Ultra Antivirus in Enterprise Security
For business environments, ultra antivirus solutions serve as critical components within comprehensive security architectures. Enterprise deployments require capabilities beyond individual protection, including centralized management, detailed threat reporting, compliance support, and integration with broader security ecosystems.
Centralized Management and Deployment
Enterprise ultra antivirus solutions provide centralized management consoles that allow IT administrators to oversee security across hundreds or thousands of endpoints from a single interface. These management platforms enable mass installation and configuration, ensuring consistent security policies across the entire organization without requiring individual attention to each computer.
Key centralized management capabilities include policy enforcement, where administrators define security settings, scanning schedules, and response protocols that are automatically applied to all managed endpoints. This ensures organizational security standards are maintained consistently regardless of user behavior or individual preferences. Remote updates allow administrators to deploy security patches, definition updates, and software upgrades across the entire fleet simultaneously, closing security gaps organization-wide within minutes rather than days or weeks.
Advanced enterprise solutions also provide role-based access controls, allowing different administrators to manage specific endpoint groups or security functions based on their responsibilities. This hierarchical management structure proves essential in large organizations with distributed IT teams.

Furthermore, enterprise ultra antivirus platforms often include automated deployment tools that integrate with existing IT management systems such as Active Directory, SCCM, or Group Policy, streamlining the process of protecting new computers as they join the network. This automation reduces administrative overhead while ensuring no endpoints remain unprotected.
Advanced Threat Reporting and Analytics
Enterprise environments require comprehensive visibility into security events across the organization. Ultra antivirus solutions designed for business use provide detailed logs and reports that document every security event, including detected threats, quarantined files, scanning activities, policy violations, and system changes.
These reporting capabilities serve multiple critical functions. For security audits, detailed logs provide evidence of security controls and incident responses required by compliance frameworks and internal security policies. During incident response, comprehensive event timelines help security teams understand attack vectors, identify compromised systems, and assess the scope of breaches.
Advanced analytics dashboards aggregate security data across the enterprise, identifying trends such as which threat types are most prevalent, which departments experience the most security events, or which systems may be particularly vulnerable. These insights enable proactive security improvements and resource allocation decisions.
Many enterprise ultra antivirus solutions offer integration with Security Information and Event Management (SIEM) systems, feeding security events into broader monitoring platforms that correlate data from multiple sources including firewalls, intrusion detection systems, and authentication logs. This integration provides holistic security visibility and enables sophisticated threat detection that recognizes attack patterns spanning multiple systems and security layers.
Supporting Regulatory Compliance
Organizations across various industries face stringent regulatory requirements regarding data protection and cybersecurity. Ultra antivirus solutions contribute to compliance with standards such as GDPR, HIPAA, PCI DSS, SOX, and industry-specific regulations by providing technical controls and documentation required by these frameworks.
For example, GDPR requires organizations to implement "appropriate technical and organizational measures" to protect personal data. Deploying ultra antivirus across all systems that process personal data helps satisfy this requirement by demonstrating proactive security measures. The detailed logging and reporting capabilities provide audit trails documenting security controls and incident responses, essential for demonstrating compliance during regulatory audits.
HIPAA-covered entities must implement technical safeguards to protect electronic protected health information (ePHI). Ultra antivirus solutions help meet requirements for malware protection, access controls, and audit controls specified in the HIPAA Security Rule. Similarly, PCI DSS requirement 5 explicitly mandates deployment of antivirus software on all systems commonly affected by malware, with regular updates and active scanning.
According to 2025 compliance data, organizations with comprehensive endpoint protection including ultra antivirus solutions experience 40-50% fewer compliance violations related to data security compared to those with basic or inconsistent protection. The automated policy enforcement and centralized management capabilities of enterprise ultra antivirus solutions ensure security controls remain consistently applied across all systems, reducing compliance risks associated with configuration drift or human error.
Optimizing System Performance with Ultra Antivirus
A distinguishing characteristic of ultra antivirus solutions is their dual focus on security and system performance. Rather than viewing these as competing priorities, leading solutions recognize that optimal security requires well-maintained, efficiently operating systems. The integration of system optimization tools within ultra antivirus software delivers comprehensive digital health management.
Disk Cleanup and Storage Management
Over time, computers accumulate substantial amounts of unnecessary data that consumes storage space and potentially harbors security risks. Ultra antivirus solutions include disk cleanup features that identify and remove several categories of redundant data:
Temporary files created by applications and the operating system during normal operation often remain on disk long after they're needed, consuming gigabytes of space. Browser cache and cookies store web content locally to speed page loading but can accumulate to hundreds of megabytes or more, and may contain tracking data that compromises privacy. System logs and error reports document system events but typically serve no ongoing purpose for end users. Recycle bin contents and Windows update backup files represent additional categories of data that can be safely removed.
Effective disk cleanup can recover 5-20GB or more of storage space on typical systems, and in some cases much more on computers that haven't been maintained regularly. Beyond freeing space, cleanup eliminates potential hiding places where malware might conceal itself among legitimate temporary files, and improves system responsiveness by reducing disk fragmentation and file system complexity.
Advanced storage management features also identify large or duplicate files, helping users make informed decisions about what to keep, archive, or delete. Some ultra antivirus solutions provide recommendations for files that can be safely removed based on age, file type, and usage patterns.
Startup and Process Management
System boot time and overall responsiveness are significantly impacted by programs configured to launch automatically at startup. Many applications add themselves to startup without user awareness, resulting in dozens of programs loading simultaneously when the computer boots. This creates lengthy boot times and consumes system resources even when these programs aren't actively being used.
Ultra antivirus solutions include startup management tools that provide visibility into all programs configured to launch at boot, allowing users to disable unnecessary items. Reducing startup programs can decrease boot times from several minutes to under 30 seconds on modern systems, and frees memory and CPU resources for applications users actually want to run.
Process management features extend this optimization to running applications, providing real-time monitoring of CPU, memory, and disk usage by each active process. Users can identify resource-hogging applications and make informed decisions about whether to close them, adjust their settings, or seek more efficient alternatives. Some ultra antivirus solutions automatically detect and offer to terminate unresponsive processes that are consuming resources without performing useful work.
These optimization capabilities prove particularly valuable on older computers or systems with limited hardware resources, where careful resource management can significantly extend the useful life of the hardware.
Regular Maintenance and Health Checks
Consistent system maintenance proves essential for long-term computer health and security. Ultra antivirus solutions facilitate this through scheduled scans and automatic optimization routines that run at predetermined intervals without requiring user intervention.
Administrators can configure weekly or monthly full system scans during off-hours, ensuring comprehensive malware detection without interrupting work. Automatic cleanup routines can be scheduled to remove temporary files, clear browser caches, and optimize system settings on a regular basis, preventing the accumulation of digital clutter that degrades performance over time.
Many ultra antivirus solutions provide system health dashboards that present at-a-glance status of key metrics including malware protection status, system optimization level, disk space availability, and security vulnerabilities. These dashboards often include actionable recommendations such as "Run disk cleanup to free 8GB of space" or "3 programs are slowing startup—disable recommended items."
| Ultra Antivirus Solution | Disk Cleanup | Startup Management | Process Monitoring | Scheduled Optimization | Health Dashboard |
|---|---|---|---|---|---|
| 360 Total Security | Comprehensive multi-category cleanup | Detailed startup control | Real-time resource monitoring | Customizable schedules | Intuitive visual dashboard |
| Premium Solution A | Basic cleanup features | Standard startup management | Limited process info | Fixed schedules | Text-based reports |
| Premium Solution B | Advanced cleanup with recommendations | Intelligent startup optimization | Detailed process analytics | AI-optimized scheduling | Comprehensive dashboard |
| Free Solution C | Limited cleanup (upgrade required) | Basic startup view | Not included | Manual only | Minimal information |
360 Total Security stands out in this category by providing comprehensive optimization features in its free version, including all cleanup, startup management, and health monitoring capabilities without artificial restrictions. This makes it an excellent choice for users seeking both robust security and system performance enhancement without ongoing costs.
Future of Ultra Antivirus and Cybersecurity Trends
The cybersecurity landscape continues to evolve rapidly, driven by technological advancement, changing threat actor tactics, and the expanding attack surface created by digital transformation. Ultra antivirus solutions are evolving in parallel, incorporating emerging technologies and expanding their protective scope to address future challenges.
The Increasing Role of Artificial Intelligence
Artificial intelligence will play an increasingly central role in ultra antivirus solutions through 2026 and beyond. Current AI implementations focus primarily on threat detection, but future systems will extend AI capabilities to predictive threat analysis and automated response mechanisms.
Predictive analysis leverages machine learning models trained on historical attack data to forecast emerging threat trends before they become widespread. By identifying early indicators of new attack campaigns—such as subtle changes in malware behavior patterns or novel exploitation techniques appearing in isolated incidents—AI systems can prepare defenses proactively rather than reacting after threats become prevalent.
Automated response mechanisms represent another frontier in AI-enhanced security. Rather than simply alerting users to threats, future ultra antivirus solutions will autonomously execute response protocols including isolating compromised systems, blocking malicious network connections, reverting unauthorized system changes, and initiating remediation procedures. This automation proves essential as attack speeds increase and the window for effective human response narrows.
According to Dr. James Chen, a cybersecurity futurist and AI researcher: "The next generation of endpoint security will be characterized by autonomous systems that not only detect threats but understand their context, predict their evolution, and respond adaptively without human intervention. We're moving from reactive tools to intelligent agents that actively defend systems."
Natural language processing capabilities will enable ultra antivirus solutions to analyze threat intelligence reports, security advisories, and even dark web communications to extract actionable insights about emerging threats. This contextual understanding will allow security systems to anticipate attacks based on threat actor discussions and preparations rather than waiting for actual attack attempts.
Cloud-Based Security and Collective Intelligence
The architecture of ultra antivirus solutions is shifting toward cloud-based security models that leverage distributed computing power and collective intelligence. This approach offers several significant advantages over traditional locally-installed security software.
Cloud-based threat intelligence aggregates security data from millions of endpoints worldwide, creating a global threat detection network. When any protected system encounters a new threat, that intelligence is instantly shared across the entire user base, dramatically reducing the window of vulnerability. According to 2026 industry analysis, cloud-connected security solutions detect and respond to emerging threats 10-15 times faster than isolated systems relying solely on local definition updates.
The shift toward lightweight clients with heavy cloud backends allows resource-intensive analysis to be offloaded to powerful cloud infrastructure rather than consuming local system resources. Client software becomes progressively thinner, focusing on monitoring and data collection while complex threat analysis, machine learning processing, and pattern recognition occur in the cloud. This architecture enables even modest computers to benefit from enterprise-grade security analysis without performance degradation.
Cloud-based security also facilitates continuous updates and improvements without requiring user intervention or software reinstallation. New detection algorithms, updated threat signatures, and enhanced analysis capabilities can be deployed instantly to all users, ensuring everyone benefits from the latest protection without update delays or compatibility issues.
Privacy considerations remain important in cloud-based architectures, and leading ultra antivirus providers implement privacy-preserving techniques such as anonymization, differential privacy, and local processing of sensitive data to balance security effectiveness with user privacy protection.
Expanding Protection to IoT and Network Edges
While this article focuses primarily on desktop security, the future of ultra antivirus extends beyond traditional computers to encompass the broader digital ecosystem. The proliferation of Internet of Things (IoT) devices and the expansion of network edges create new security challenges that future ultra antivirus solutions will address.
Smart home devices, network-attached storage, routers, and other connected devices often lack robust built-in security and can serve as entry points for attackers to compromise entire networks. Future ultra antivirus solutions will extend protection to these network peripherals, monitoring device behaviors, detecting compromised IoT devices, and preventing lateral movement from compromised peripherals to critical systems.
Network-level protection capabilities will become standard features in ultra antivirus solutions, providing visibility into all devices connected to home or business networks and identifying suspicious communications or vulnerable devices. This holistic approach recognizes that effective security requires protecting the entire digital ecosystem rather than individual computers in isolation.
Integration between endpoint security, network security, and cloud security will create unified protection frameworks where ultra antivirus solutions serve as central coordination points for comprehensive digital security. This convergence reflects the reality that modern computing involves complex interactions between local systems, cloud services, and network infrastructure, all of which require coordinated protection.
As we progress through 2026 and beyond, ultra antivirus will continue evolving from isolated endpoint protection tools into intelligent, cloud-connected, AI-powered security platforms that protect entire digital ecosystems proactively and autonomously.
Frequently Asked Questions
What is the difference between regular antivirus and ultra antivirus?
Ultra antivirus solutions go significantly beyond basic malware detection offered by regular antivirus software. While traditional antivirus primarily relies on signature-based detection of known threats, ultra antivirus incorporates multiple advanced technologies including behavioral analysis, machine learning, heuristic detection, and cloud-based threat intelligence to identify both known and unknown threats. Additionally, ultra antivirus typically includes system optimization features, vulnerability scanning, advanced web protection, and more sophisticated threat response capabilities. The "ultra" designation indicates a comprehensive, multi-layered security approach rather than single-purpose malware detection.
Can free ultra antivirus software provide adequate protection?
Yes, several free ultra antivirus solutions provide excellent protection suitable for home users and even some business applications. The key is distinguishing between genuinely robust free solutions and limited "freemium" offerings that restrict essential features. 360 Total Security exemplifies a world-class free solution that delivers comprehensive malware protection, real-time threat detection, system optimization tools, and regular updates without artificial feature limitations. For many users, a quality free solution provides all necessary protection without ongoing subscription costs. However, enterprise users or those requiring advanced features like VPN, password management, or priority support may benefit from paid solutions.
How much system resources does ultra antivirus typically consume?
Modern ultra antivirus solutions are designed with efficiency in mind and typically consume minimal system resources. During normal operation, quality ultra antivirus software uses approximately 1-2% of CPU resources and 150-250MB of RAM on average systems. Full system scans are more resource-intensive but can be scheduled during idle periods to avoid impacting productivity. Cloud-assisted scanning architectures further reduce local resource consumption by offloading intensive analysis to remote servers. Users with older computers or limited hardware should look for solutions specifically optimized for lightweight operation, and can further minimize impact through configuration settings that balance protection intensity with performance requirements.
Do I need ultra antivirus if I only visit trusted websites and don't download suspicious files?
Yes, ultra antivirus remains essential even for cautious users. Modern cyber threats extend far beyond suspicious downloads and can compromise systems through multiple vectors including drive-by downloads from legitimate but compromised websites, malicious advertisements on trusted sites, vulnerabilities in installed software, phishing emails that appear to come from legitimate sources, and zero-day exploits that target unpatched software. According to 2026 security research, approximately 40% of malware infections occur through legitimate websites that have been compromised or through exploitation of software vulnerabilities rather than user-initiated downloads. Ultra antivirus provides critical protection against these diverse threat vectors that careful browsing habits alone cannot prevent.
Author Bio
This article was authored by the cybersecurity content team at 360 Total Security, drawing on over a decade of experience in endpoint protection, threat intelligence, and system optimization. Our team includes certified security professionals, malware researchers, and technical writers dedicated to making complex cybersecurity concepts accessible to users worldwide. We continuously monitor emerging threats, analyze industry trends, and test security solutions to provide accurate, actionable guidance for protecting digital assets in an evolving threat landscape.
Learn more about 360 Total Security