May 6, 2026
360 Security Center
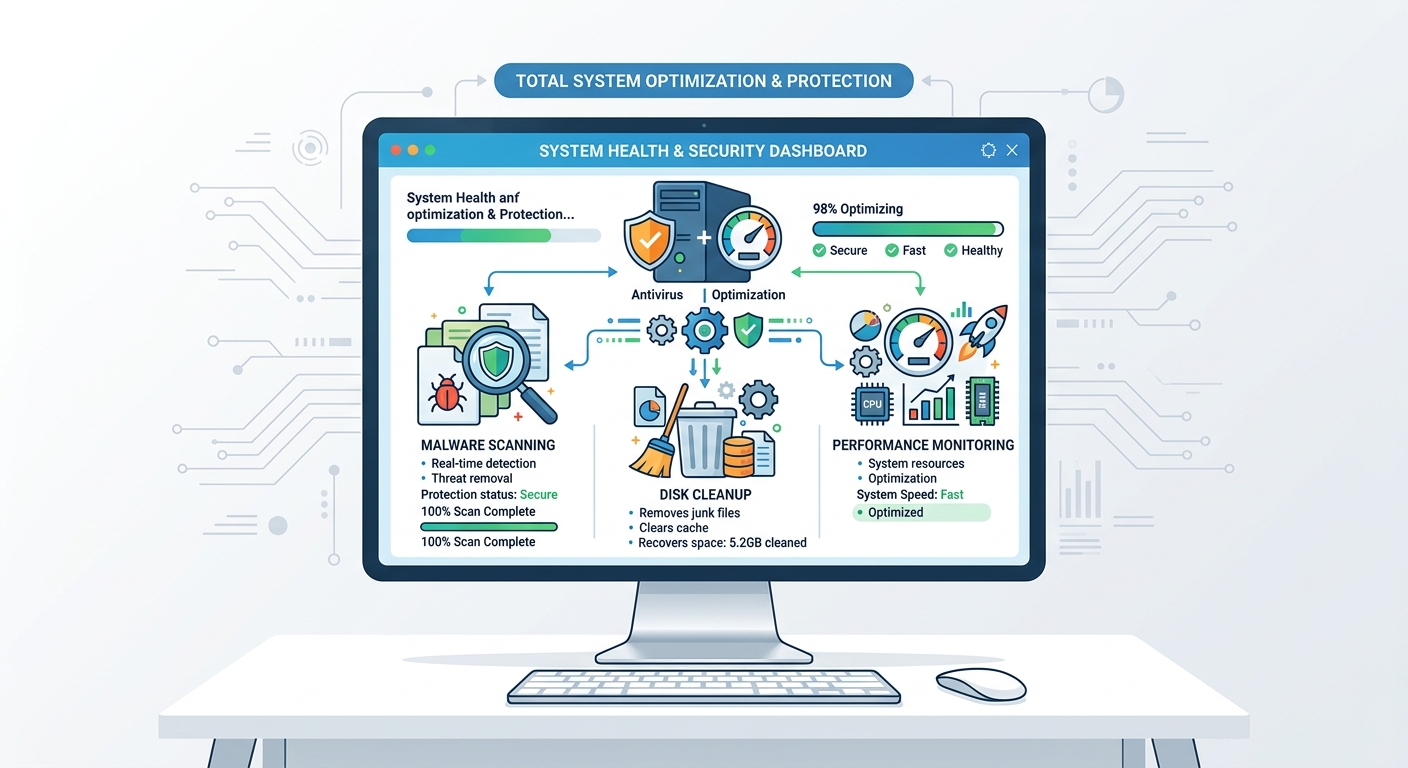
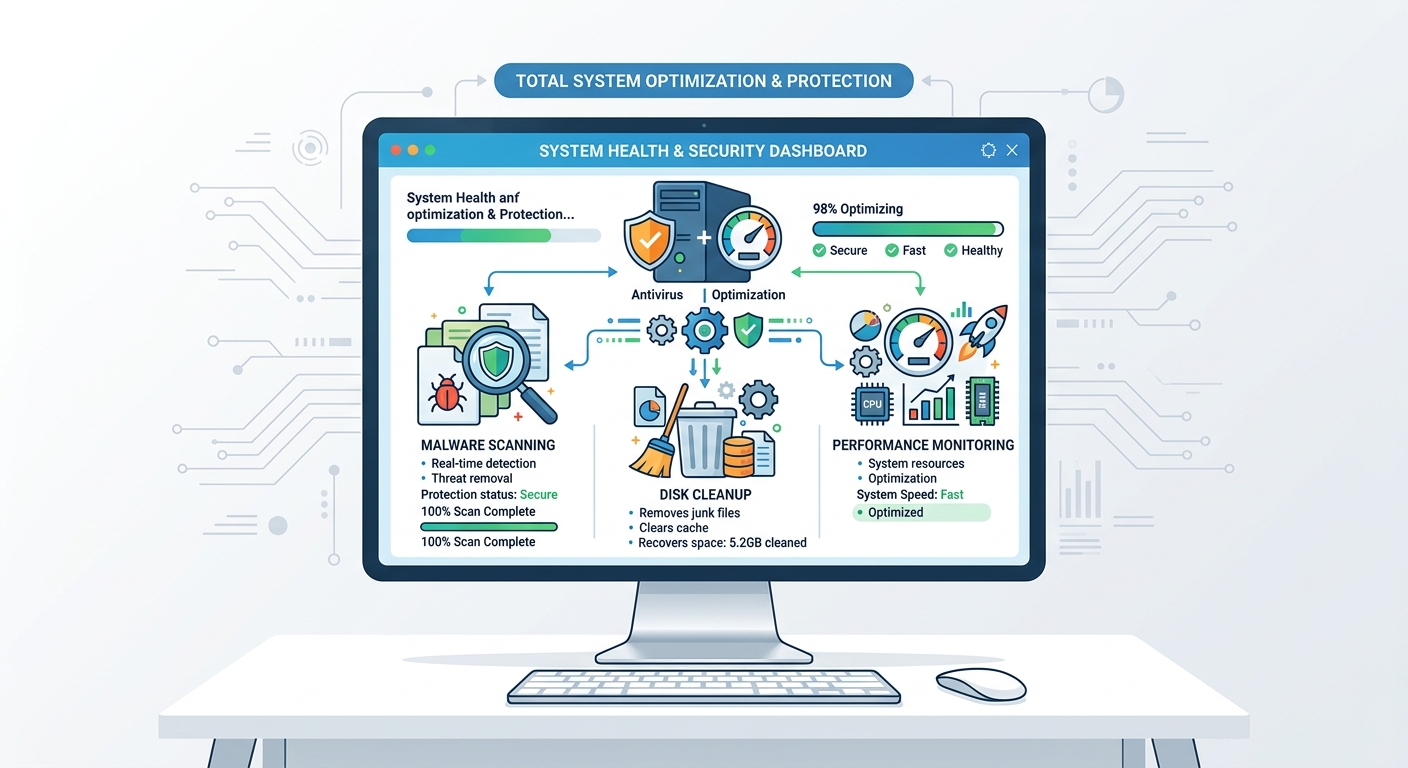
Executive Summary: Achieving a consistently fast and secure PC is not a one-time event but an ongoing discipline that demands the right combination of intelligent tools, proactive habits, and a struct...
May 6, 2026
360 Security Center
Executive Summary: In today's rapidly evolving cybersecurity landscape, the term "ultra antivirus" represents a new generation of security solutions that transcend traditional malware detection. Ultra...
May 6, 2026
360 Security Center
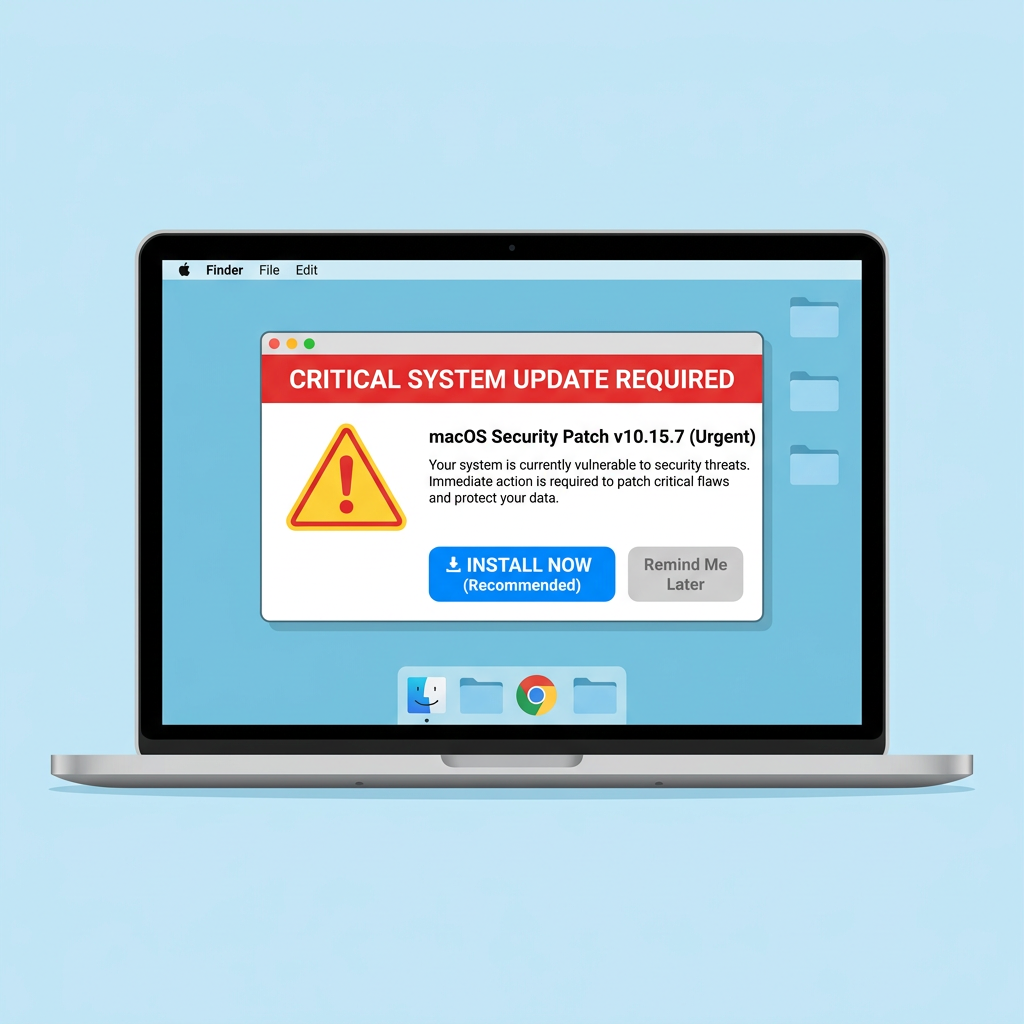
The Nvir Mac virus represents a growing threat to macOS users, exploiting both technical vulnerabilities and human psychology to compromise system integrity. As Mac market share expands in business an...
May 6, 2026
360 Security Center
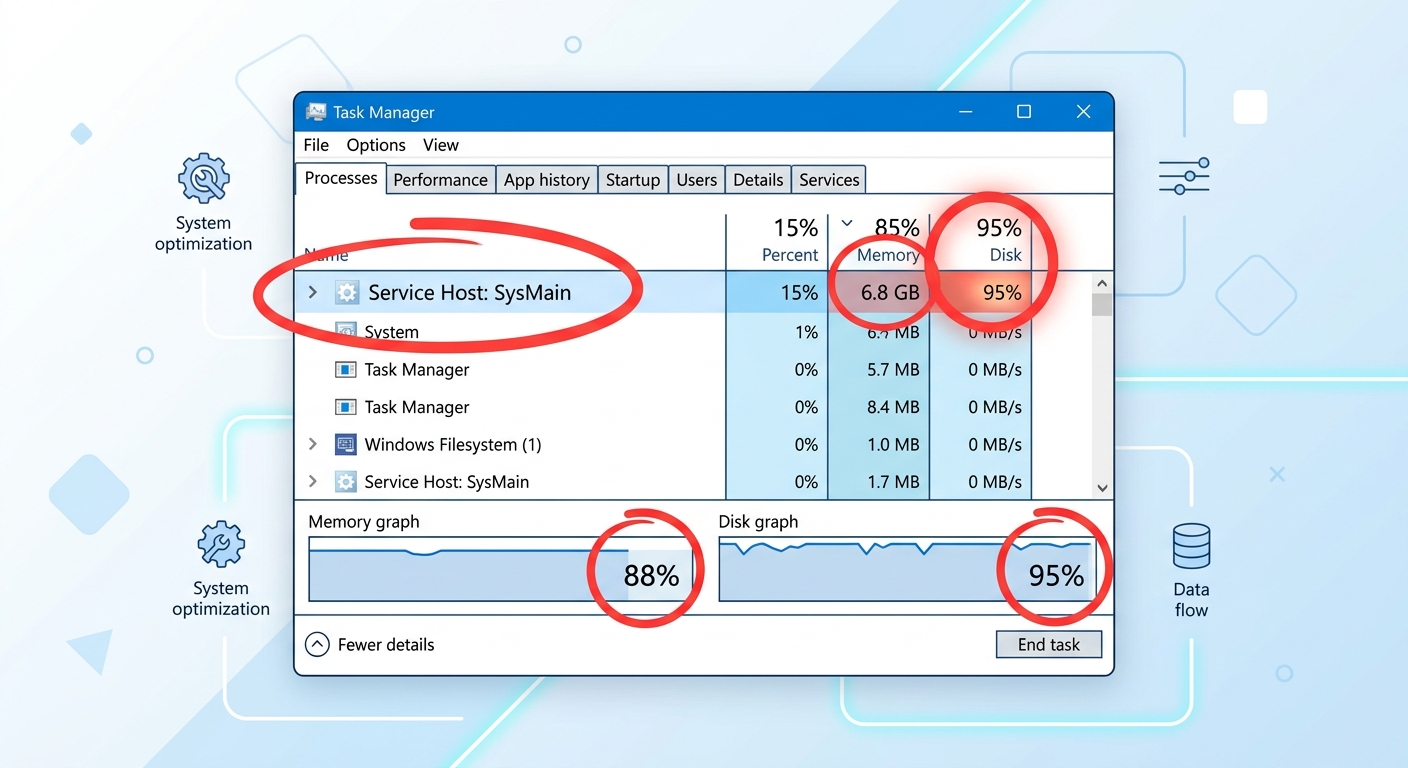
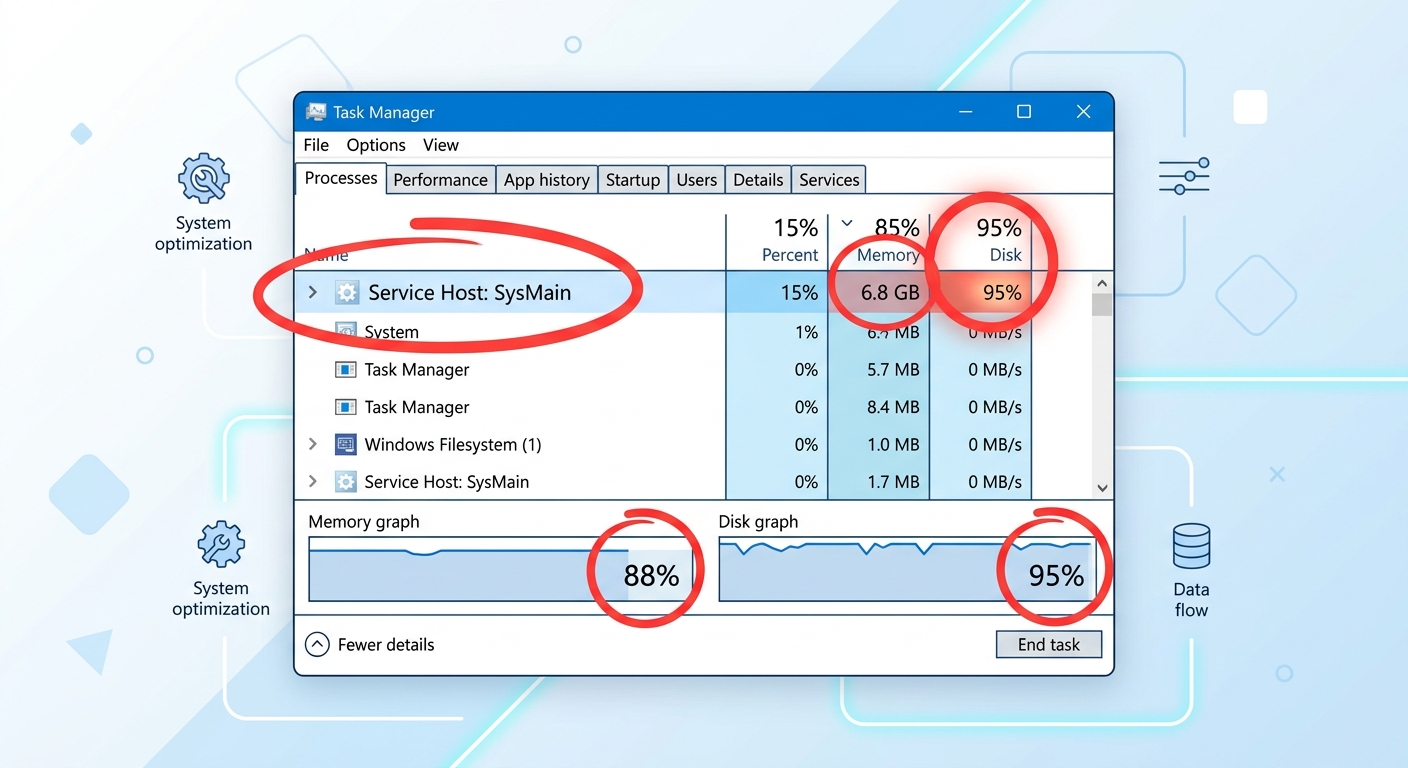
Executive Summary: Modern PCs equipped with cutting-edge processors, abundant RAM, and fast SSDs should deliver lightning-fast performance. Yet countless users experience frustrating slowdowns, applic...

May 6, 2026
360 Security Center
Computer viruses and malware represent one of the most persistent threats to digital security in 2025. Understanding how to identify, confirm, and eliminate these threats is essential for maintaining ...
May 6, 2026
360 Security Center
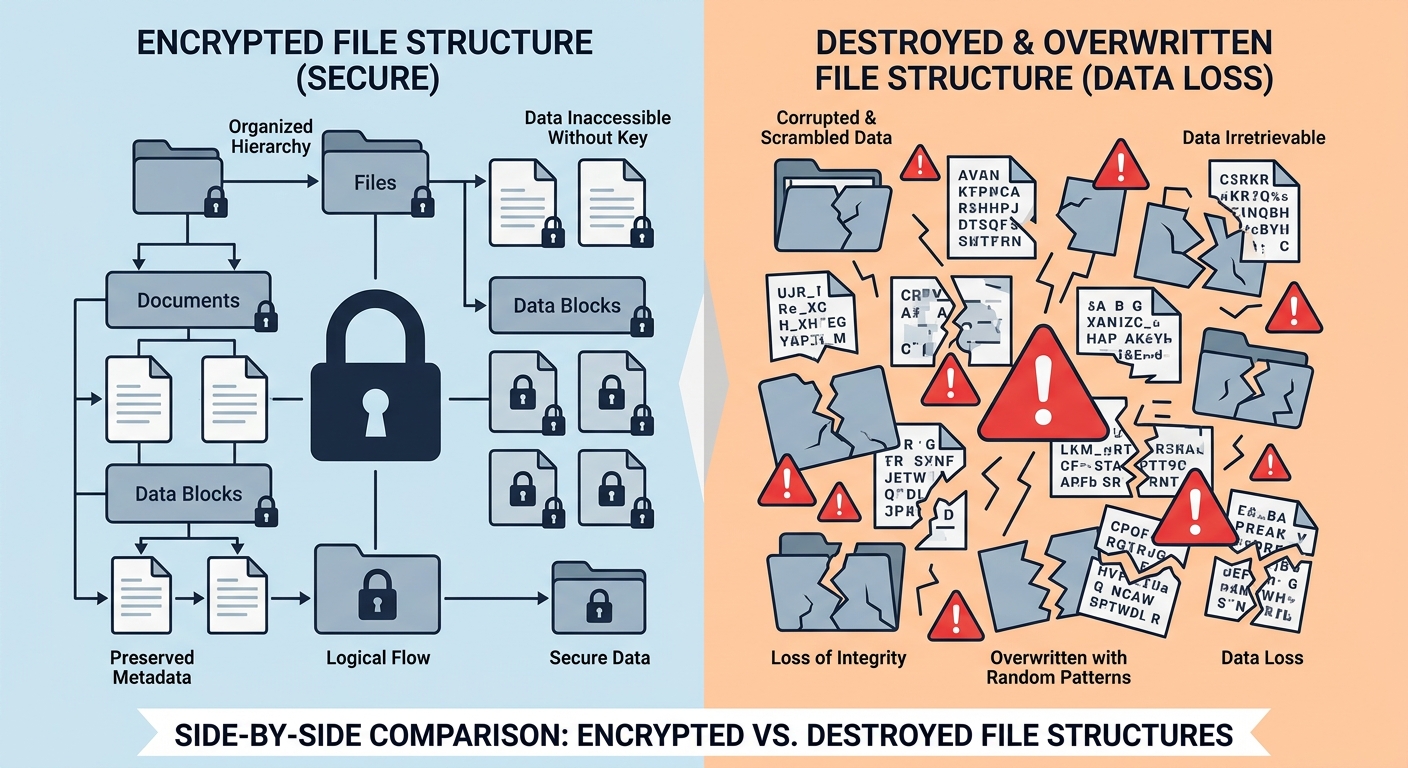
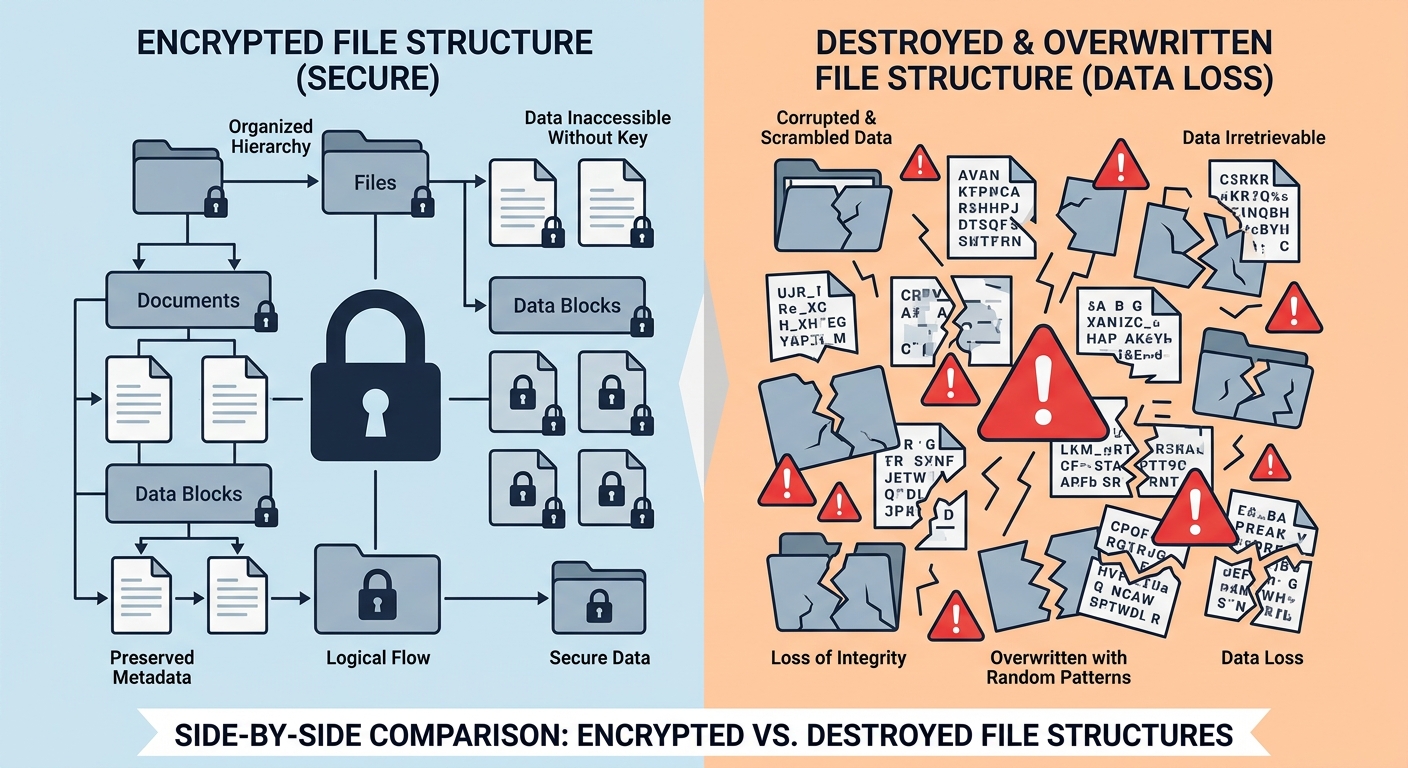
Executive Summary: A dangerous new category of ransomware has emerged that abandons traditional encryption tactics in favor of permanent, irreversible file destruction. Unlike conventional ransomware ...
May 6, 2026
360 Security Center
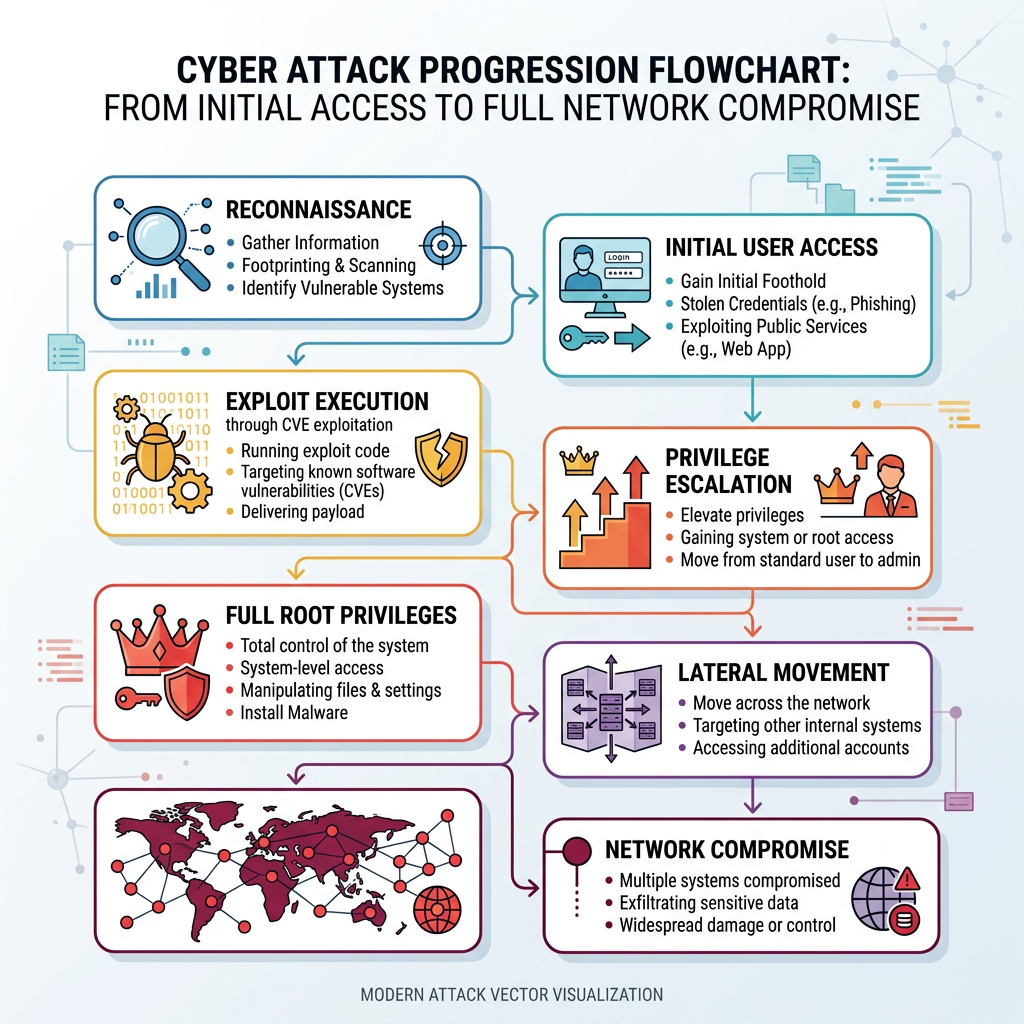
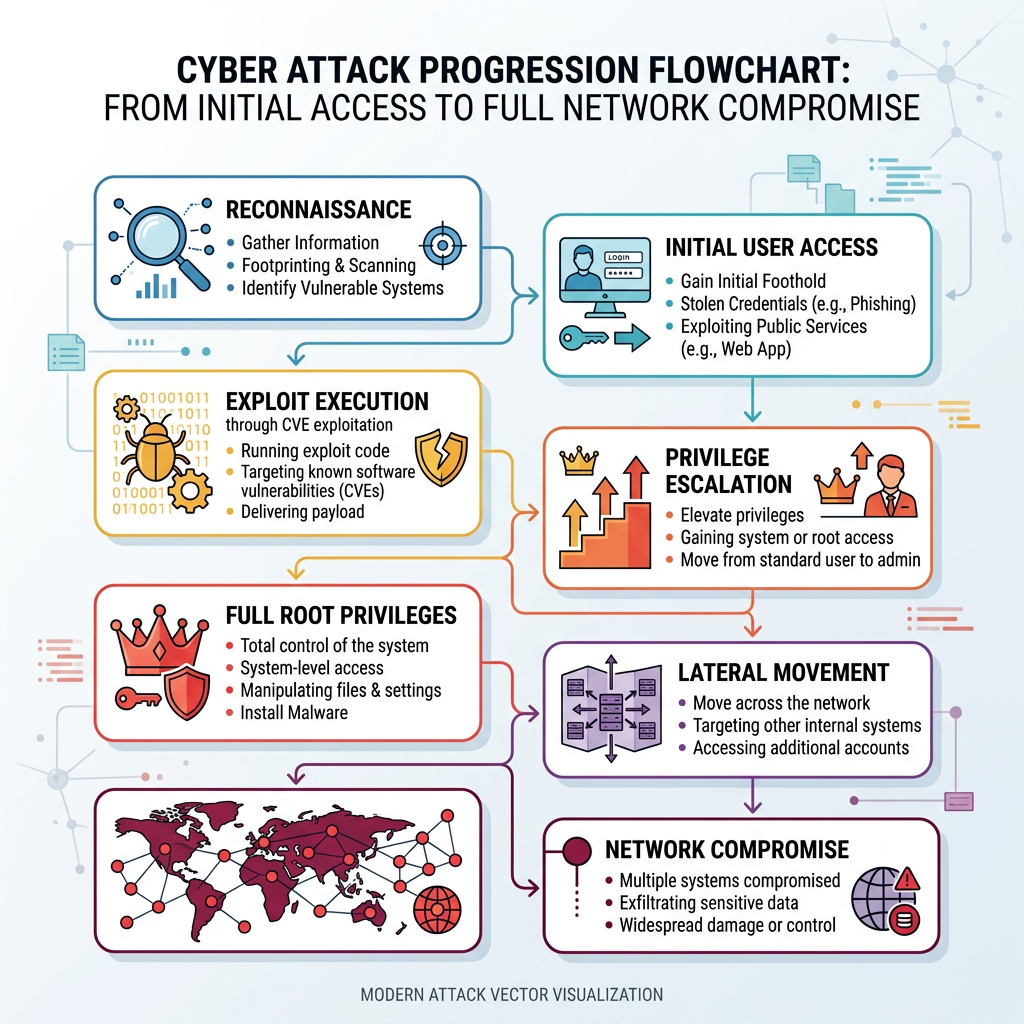
Executive Summary: Critical Linux CVE vulnerabilities that enable root privilege escalation represent the most severe category of security threats facing enterprise and personal computing infrastructu...

May 6, 2026
360 Security Center
In today's interconnected digital landscape, mobile devices have become primary targets for cybercriminals. This comprehensive guide explores the critical warning signs of phone malware infections, pr...
May 6, 2026
360 Security Center
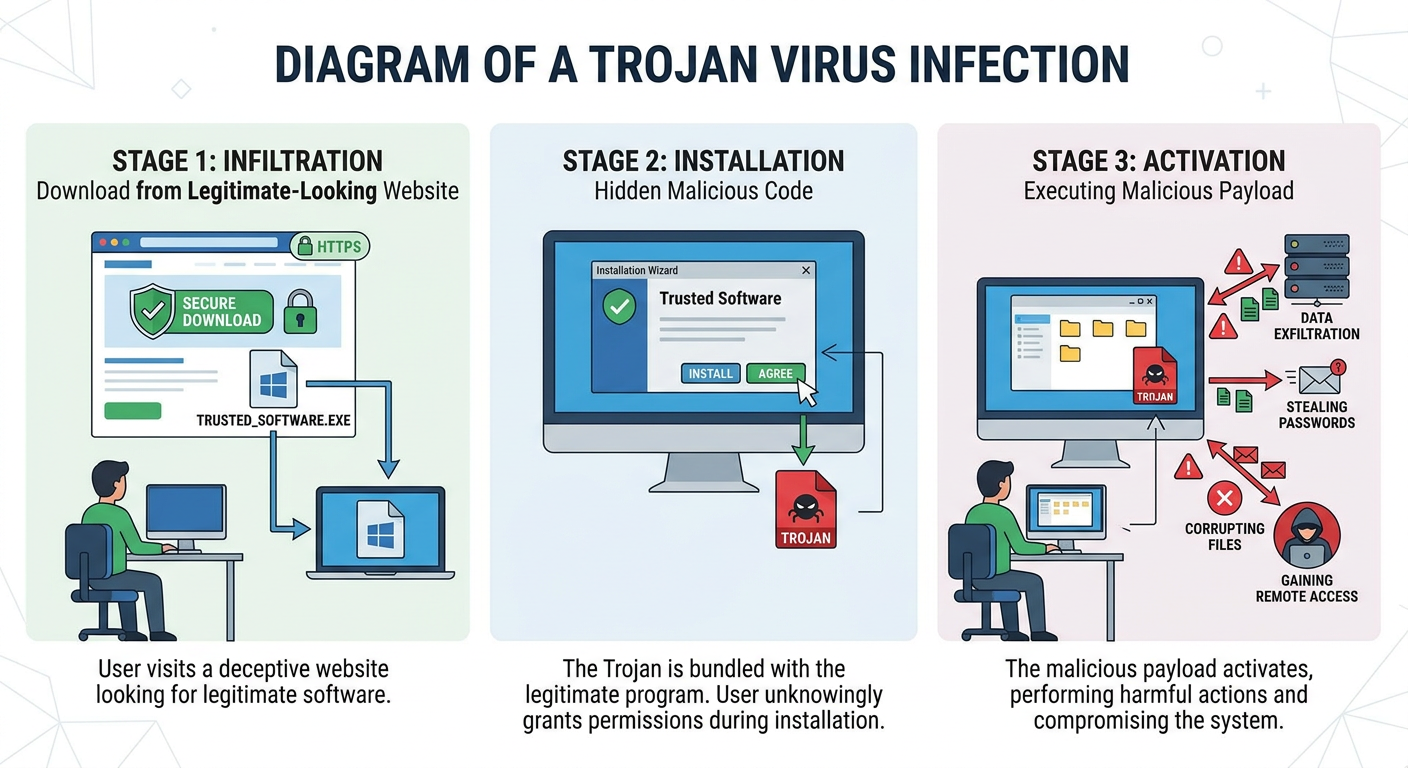
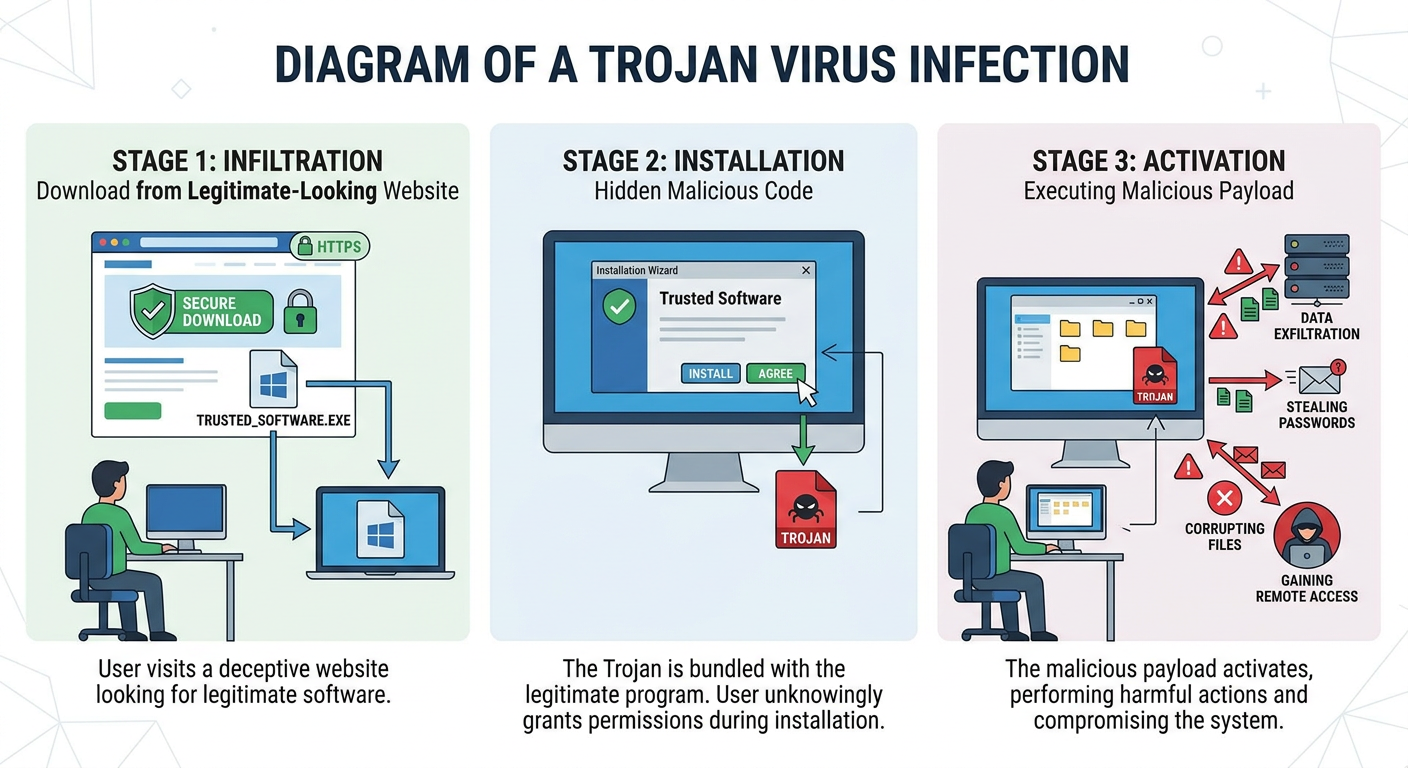
Executive Summary: Trojan viruses represent one of the most deceptive and persistent cybersecurity threats facing modern computer users. Unlike traditional malware that announces its presence, Trojans...
May 6, 2026
360 Security Center
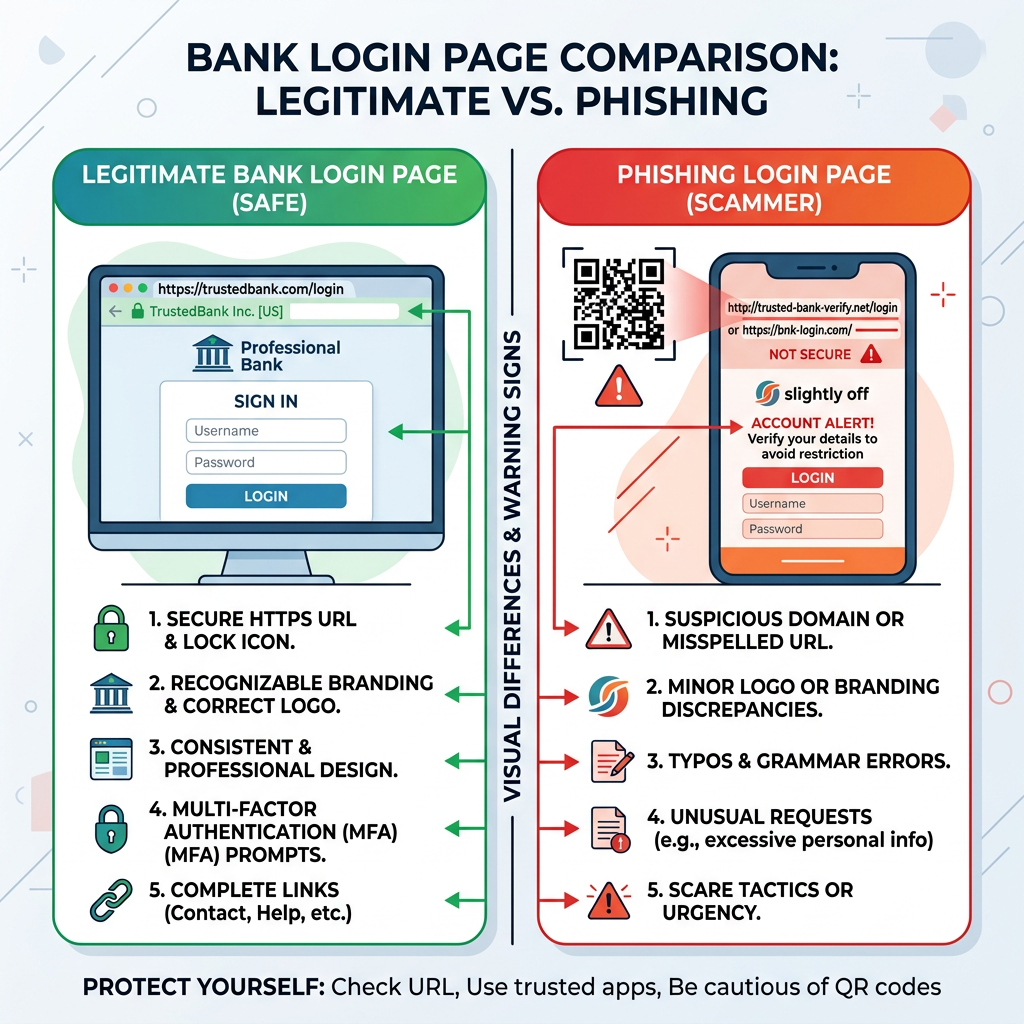
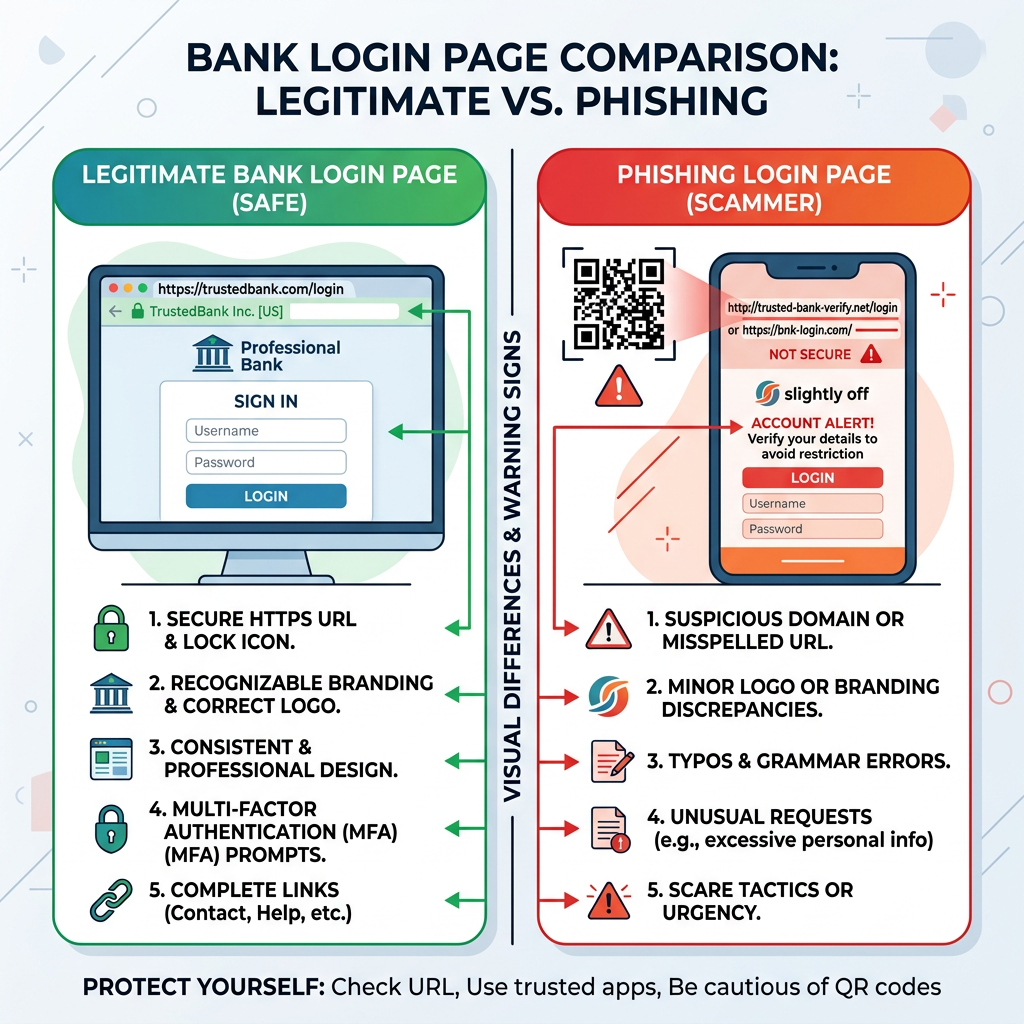
Executive Summary: QR codes have become ubiquitous in our daily lives, offering convenient access to websites, payment systems, and digital content. However, this convenience has created a lucrative o...